
News of the Claude Code source code leak has spread across the entire internet. Since the leak occurred on March 31, 2026, it has gone viral on Twitter, LinkedIn, and developer forums. Security researchers, open‑source enthusiasts, and curious developers have been sharing links, analyzing the exposed code, and even backing up the leaked files to their own GitHub repositories before takedown notices could remove them.
What started as a simple configuration mistake inside Anthropic’s npm package quickly turned into one of the biggest source code exposures in the AI tooling space. The leaked material includes the full TypeScript source of the proprietary Claude Code CLI—over 500,000 lines of code that reveal how the tool manages commands, coordinates multiple agents, handles permissions, and even some features that hadn’t been publicly announced yet.
In the hours since the leak, GitHub repos hosting the original code have been hit with DMCA takedowns, but developers have already begun rewriting the system in Python and Rust, arguing that clean‑room implementations are legally distinct from the original.
How Did the Leak Happen?
The leak wasn’t a sophisticated hack. It was a simple configuration oversight.
Anthropic published the Claude Code CLI as an npm package (the standard way to distribute Node.js tools). When they built the package, they included source map files (.map files). Source maps are normally used to help debug minified code, but they can sometimes contain the original source code in a readable form.
In this case, the source maps pointed directly to an unobfuscated ZIP archive stored in Anthropic’s own R2 (Cloudflare’s object storage) bucket. That ZIP contained the full TypeScript source code of Claude Code—nearly 1,900 files and over 500,000 lines of code.
Security researcher Chaofan Shou (@Fried_rice) discovered the leak and shared it publicly. By the time Anthropic pulled the files, the source code had already been downloaded and mirrored across the internet.
What Was Exposed
The leaked code was far more than a few helper functions. It included the entire TypeScript source of the Claude Code CLI, spanning over 50 slash commands that form the tool’s main interactions. Beyond that, the leak exposed the multi‑agent coordination system, the React and Ink terminal UI components, and the IDE bridge integration. It also revealed the permission engine and security logic, cost tracking and session memory systems, and even a handful of unreleased features that hadn’t been announced yet. In short, the full blueprint of how Claude Code works internally became public overnight.
The Aftermath: DMCA Takedowns and Clever Workarounds
Within hours, Anthropic started issuing DMCA takedown notices to GitHub repositories that were hosting the leaked code. That’s standard practice when proprietary code gets out.
But then something interesting happened. Developers who had downloaded the code started creating rewritten versions of Claude Code in other programming languages—specifically Python and Rust.
One notable example is Sigrid Jin (@realsigridjin). She cloned the leaked repo late at night, fell asleep, and woke up to find it had over 50,000 stars on GitHub Repo. Her girlfriend, a copyright lawyer, suggested that simply hosting the original code was risky. So the team decided to rewrite the entire system in Python, using the leaked code as a reference. That, they argued, was a clean‑room reimplementation and legally distinct from the original.
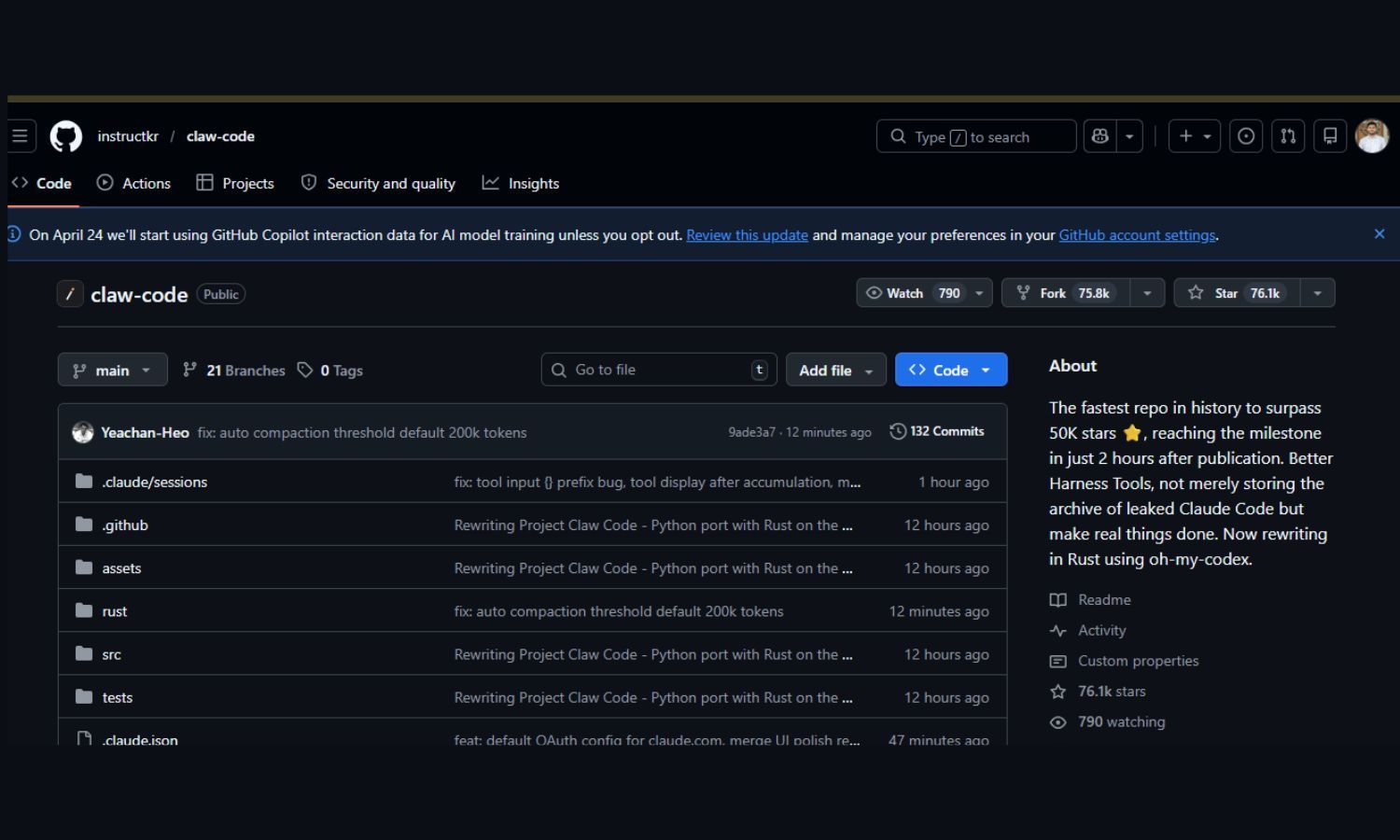
Soon after, another developer, @bellman_ych, teamed up with Sigrid to create clawd-code a Rust rewrite of the same architecture. Because it’s a reimplementation, not a copy, it’s much harder for Anthropic to take down.
What Should Developers Do?
If you’re a user of Claude Code, you are not at risk from this leak. The leak exposed the source code, not user data or API keys. The CLI itself remains safe to use.
If you’re a developer who downloaded the leaked code, be aware that hosting the original files may expose you to DMCA claims. But studying the code to understand how a sophisticated AI‑powered CLI works is not illegal—just be mindful of copyright.
And if you’re building your own tools, this is a good reminder to audit your build and publish pipelines. Double‑check your .npmignore or .gitignore files. Run a quick test after publishing to ensure no stray source maps or internal assets are publicly accessible.
Read more

Where Is Stolen Data Typically Bought and Sold? Inside the Dark Web Economy
Where is stolen data typically bought and sold? On dark web markets. Learn how the underground economy works, what data is traded, and how to protect yourself.

The Axios Security Scare: What Developers Need to Know
Learn the truth behind the 2026 Axios security incident: what happened, how to check if you're affected, and the simple steps to stay safe.

Passkeys, AI Scams, and Data Leaks: The New Cybersecurity Reality in 2026
Cybersecurity threats are evolving rapidly in 2026. From AI-powered scams to the rise of passkeys replacing passwords, here’s how individuals and businesses can protect their data, privacy, and digital identity in today’s increasingly hostile online world.